How does the meet-in-the-middle attack work?
How does the meet-in-the-middle attack work?
A Meet-in-the-Middle (MitM) Attack is a kind of cryptanalytic attack where the attacker uses some kind of space or time tradeoff to aid the attack. Specifically, MitMs attempt to reduce the amount of difficulty required to carry out the assault in its original state.
What is meet-in-the-middle attack in Triple DES?
The MITM is a generic attack which weakens the security benefits of using multiple encryptions by storing intermediate values from the encryptions or decryptions and using those to improve the time required to brute force the decryption keys.
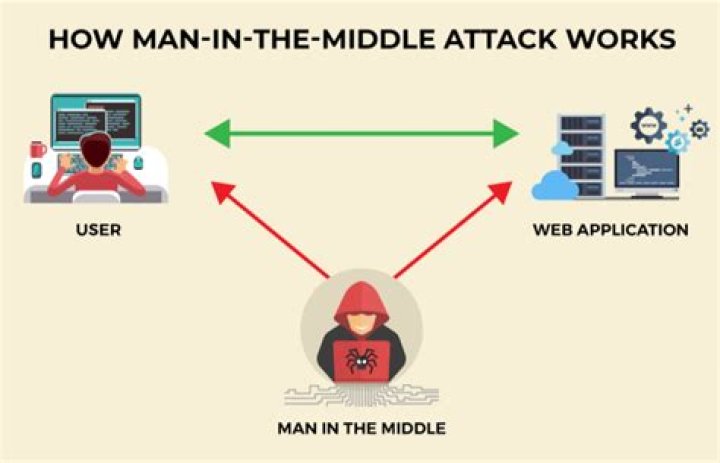
What is an example of a man in the middle attack?
One example of a MITM attack is active eavesdropping, in which the attacker makes independent connections with the victims and relays messages between them to make them believe they are talking directly to each other over a private connection, when in fact the entire conversation is controlled by the attacker.
How common are man in the middle attacks?
Though not as common as ransomware or phishing attacks, MitM attacks are an ever-present threat for organizations. IBM X-Force’s Threat Intelligence Index 2018 says that 35 percent of exploitation activity involved attackers attempting to conduct MitM attacks, but hard numbers are difficult to come by.
What is a meet-in-the-middle attack in double DES algorithm?
Meet-in-the-middle attacks are often executed to decode multiple data encryption standard (DES) techniques. A double DES, for example, uses two encryption keys to transform its plaintext inputs into ciphertext outputs. This method of encryption uses its two unique keys to perform two encryption stages.
What is the idea behind meet-in-the-middle attack how it can be avoided in 3DES?
The intruder has to know some parts of plaintext and their ciphertexts. Using meet-in-the-middle attacks it is possible to break ciphers, which have two or more secret keys for multiple encryption using the same algorithm. For example, the 3DES cipher works in this way.
Can we meet in the middle meaning?
The primary idiomatic meaning of meet in the middle is to compromise, especially when negotiating a price. For example, if I am trying to sell a used car and I ask $10,000, and you offer me $5,000, we would “meet in the middle” by agreeing to a price of $7,500.
What is the idea behind meet in the middle attack how it can be avoided in 3DES?
What causes a man-in-the-middle attack?
A man-in-the-middle attack occurs when the communication between two systems is intercepted by a third party, aka a Man-in-the-Middle. This can happen in any form of online communication, such as email, web browsing, social media, etc.
What is the effect of man-in-the-middle attack?
A man-in-the-middle attack (MITM attack) is a cyber attack where an attacker relays and possibly alters communication between two parties who believe they are communicating directly. This allows the attacker to relay communication, listen in, and even modify what each party is saying.
Does a VPN protect against man in the middle?
Does a VPN help protect against MiTM? Yes and no. Specifically, it will protect your traffic between your device and the VPN gateway, preventing your ISP (or most governments) from performing a MiTM attack targeted toward you.
Does HTTPS stop man in the middle attacks?
HTTPS connections were initially used to secure transactions that involved money and sensitive content. HTTPS is vital in preventing MITM attacks as it makes it difficult for an attacker to obtain a valid certificate for a domain that is not controlled by him, thus preventing eavesdropping.