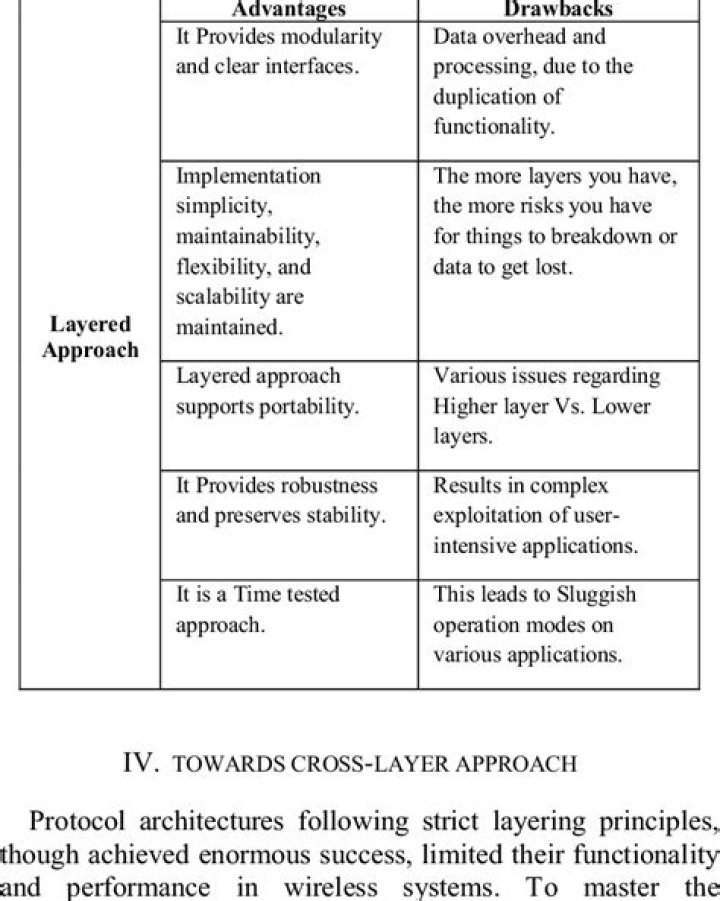
What are the advantages of layered approach?
.
Keeping this in consideration, what are the advantages of layering?
- Advantages of layered operating systems are: It is decomposable and therefore effects separation of concerns and different abstraction levels. It allows good maintenance, where you can make changes without affecting layer interfaces.
Beside above, what is the layered approach? A system can be made modular in many ways. One method is the layered approach, in which the operating system is broken up into a number of layers (levels). The bottom layer (layer 0) id the hardware; the highest (layer N) is the user interface. This approach simplifies debugging and system verification.
Likewise, people ask, what are the benefits of using a layered network model?
(Choose two.)
- It assists in protocol design.
- It speeds up packet delivery.
- It prevents designers from creating their own model.
- It prevents technology in one layer from affecting other layers.
- It ensures a device at one layer can function at the next higher layer.
What are the drawbacks for layers?
Drawbacks of a Layered Architecture:
- Lack of inbuilt scalability: The principles of layered architecture hinders the growth of your project as it does not help to scale your project.
- Hidden use cases: It is difficult to determine the use cases of your project by simply checking the code organization.
What are the disadvantages of the layered approach?
With the layered approach, the bottom layer is the hardware, while the highest layer is the user interface. The main advantage is simplicity of construction and debugging. The main difficulty is defining the various layers. The main disadvantage is that the OS tends to be less efficient than other implementations.Why is protocol layering important?
Protocol layering is a common technique to simplify networking designs by dividing them into functional layers, and assigning protocols to perform each layer's task. For example, it is common to separate the functions of data delivery and connection management into separate layers, and therefore separate protocols.Why layered approach is used in OSI model?
The primary reason for layered approach is to define the specs properly and understand the functions clearly. For example TCP/IP stack doesn't exactly match the OSI model. It has Application, Transport, Internet, and Network Access layers.Why is layering important in DTP?
Layering is an anchoring technique that can tie together many parts of a page, creating a sense of page harmony. When using layers it is important to keep in mind the foreground and background elements. The background layer is sometimes locked to prevent it from being changed accidentally.Which two tasks are functions of the presentation layer?
Explanation: The presentation layer deals with common data format. Encryption, formatting, and compression are some of the functions of the layer. Addressing occurs in the network layer, session control occurs in the session layer, and authentication takes place in the application or session layer.What is meant by layered protocol structure?
Layered Protocols. A layered protocol architecture provides a conceptual framework for dividing the complex task of exchanging information between remote hosts into simpler tasks. Each protocol layer has a narrowly defined responsibility. A protocol layer provides a standard interface to the next higher protocol layer.What are the layers in operating system?
The access layers involved include at least the organization network and firewall layers, the server layer (or physical layer), the operating system layer, the application layer, and the data structure layer.What is a system structure?
A system consists of something more than structure: it is a structure with certain properties. The structures of the organs of the body, for instance, are connected with their functions. Any breakdown in structure, any deformation of an organ leads to a distortion of the function.What are the features of operating system?
Here is a list commonly found important features of an Operating System:- Protected and supervisor mode.
- Allows disk access and file systems Device drivers Networking Security.
- Program Execution.
- Memory management Virtual Memory Multitasking.
- Handling I/O operations.
- Manipulation of the file system.
What are the 3 elements of layered security?
Layered security, as in the previous example, is known as defense in depth. This security is implemented in overlapping layers that provide the three elements needed to secure assets: prevention, detection, and response.What is the purpose of system calls?
System Calls are a way for user programs (running in user mode) to request some service from Operating System. In other words, system calls allow the user programs to ask OS to do some stuff on behalf of the user program. For example, read and write of file which requires the I/O from/to the storage device.What are the different types of operating systems?
Following are some of the most widely used types of Operating system.- Simple Batch System.
- Multiprogramming Batch System.
- Multiprocessor System.
- Desktop System.
- Distributed Operating System.
- Clustered System.
- Realtime Operating System.
- Handheld System.
What is process in operating system?
In computing, a process is the instance of a computer program that is being executed by one or many threads. Depending on the operating system (OS), a process may be made up of multiple threads of execution that execute instructions concurrently.What is the difference between microkernel and layered operating system structure?
Microkernel is the one in which user services and kernel services are kept in separate address space. However, in Monolithic kernel user services and kernel services both are kept in the same address space.Comparison Chart.
| Basis for Comparison | Microkernel | Monolithic Kernel |
|---|---|---|
| Execution | Slow execution. | Fast execution. |