IDS vs. IPS: What is the Difference? Intrusion Detection Systems (IDS) analyze network traffic for signatures that match known cyberattacks. Intrusion Prevention Systems (IPS) also analyzes packets, but can also stop the packet from being delivered based on what kind of attacks it detects — helping stop the attack..
Subsequently, one may also ask, do you need an IDS or IPS or both?
An IPS is not the same as an IDS. However, the technology that you use to detect security problems in an IDS is very similar to the technology that you use to prevent security problems in an IPS. An IPS is best compared to a firewall.
Also, what is Cisco IPS and IDS? Unlike an IDS, an IPS does not allow packets to enter the trusted side of the network. An IPS builds upon previous IDS technology; Cisco IPS platforms use a blend of detection technologies, including profile-based intrusion detection, signature-based intrusion detection, and protocol analysis intrusion detection.
Beside this, what is signature in IDS IPS?
A signature is a set of rules that an IDS and an IPS use to detect typical intrusive activity, such as DoS attacks. Sensors enable you to modify existing signatures and define new ones. As sensors scan network packets, they use signatures to detect known attacks and respond with predefined actions.
What is IPS and how does it work?
Intrusion Prevention System (IPS) helps in delivering the secure platform to the network as it proactively responds to any unauthorized threats or unwanted traffic. It has a capability to detect the threat instantly. An Intrusion Prevention System works in in-line mode.
Related Question Answers
What is IPS in firewall?
Intrusion Prevention System (IPS)- The IPS sits between your firewall and the rest of your network. Because, it can stop the suspected traffic from getting to the rest of the network. The IPS monitors the inbound packets and what they are really being used for before deciding to let the packets into the network.Is IDS active or passive?
Active and passive IDS Intrusion Detection and Prevention System (IDPS) has the advantage of providing real-time corrective action in response to an attack. A passive IDS is a system that's configured to only monitor and analyze network traffic activity and alert an operator to potential vulnerabilities and attacks.What are the different types of IPS?
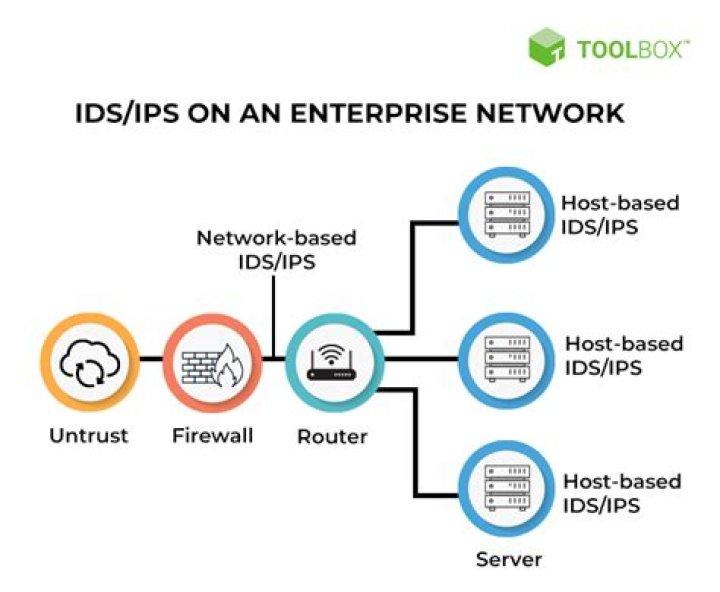
Intrusion prevention systems come in four primary types: - Network-based: Protect your computer network.
- Wireless: Protect wireless networks only.
- Network behavior: Examine network traffic.
- Host-based: Come as installed software to protect a single computer.
Why do we need IPS?
IPS/IDS serve to monitor connections for malicious activities mainly through signature based detection (similar to AV). Attacks have certain patterns and depending on your setup you can be alerted or have the system take action on those patterns.What is IPS in cyber security?
An Intrusion Prevention System (IPS) is a network security/threat prevention technology that examines network traffic flows to detect and prevent vulnerability exploits.How do IDS systems work?
Intrusion detection systems are used to detect anomalies with the aim of catching hackers before they do real damage to your network. They can be either network- or host-based. intrusion detection systems work by either looking for signatures of known attacks or deviations of normal activity.Where do I put IDS IPS?
Your IPS will generally be placed at an edge of the network, such as immediately inside an Internet firewall, or in front of a server farm. Position the IPS where it will see the bare minimum of traffic it needs to, in order to keep performance issues under tight control.What does IPS stand for?
in-plane switching
What is IDS and its types?
An intrusion detection system (IDS) is a device or software application that monitors a network or systems for malicious activity or policy violations. The most common classifications are network intrusion detection systems (NIDS) and host-based intrusion detection systems (HIDS).What does IPS protect against?
An intrusion prevention system (IPS) is a network security technology that monitors network traffic to detect anomalies in traffic flow. IPS security systems intercept network traffic and can quickly prevent malicious activity by dropping packets or resetting connections.What is the difference between a firewall and an IDS?
The main difference being that firewall preforms actions such as blocking and filtering of traffic while and IPS/IDS detects and alert a system administrator or prevent the attack as per configuration. A firewall allows traffic based on set of rules configured.How does the IDS define normal use?
An anomaly-based intrusion detection system (AIDS) monitors network traffic and compares it against an established baseline to determine what is considered normal for the network with respect to bandwidth, protocols, ports and other devices.What are drawbacks of signature based IDS?
The drawback to signature-based systems is their inability to detect new or previously unknown attacks. If no signature exists to match an attack type, the new attack will go undetected. Therefore, keeping your signature database current is important.What is one difference between the misuse and anomaly IDS models?
- They can reduce false positive rates. They can reduce false positive rates. The difference between misuse and anomaly IDS models is. - Misuse models require knowledge of normal activity, whereas anomaly models don't.How do signature based IPS work?
Signature-Based – In Signature-Based approach, predefined signatures or patterns of well-known network attacks are encoded into the IPS device by its vendors. The predefined patterns are then used to detect an attack by comparing the patterns that an attack contains, against the ones that are stockpiled in IPS.What are the two main types of intrusion detection systems?
The two main types of intrusion detection systems are network-based and host-based. Network-based systems monitor network connections for suspicious traffic. Host-based systems reside on an individual system and monitor that system for suspicious or malicious activity.What are strengths of the host based IDS?
A host-based Intrusion Detection System resides on the system being monitored and tracks changes made to important files and directories with ability to monitor events local to a host. One of the advantages of host-based IDS is that it does not have to look for patterns, only changes within a specify set of rules.What is the purpose of a honeypot IPS?
Honeypot-Based IDS/IPS Systems The purpose of the honeypot approach is to distract attacks away from real network devices. By staging different types of vulnerabilities in the honeypot server, you can analyze incoming types of attacks and malicious traffic patterns.How does Cisco IPS work?
The way that intrusion prevention systems work is by scanning network traffic as it goes across the network; unlike an intrusion detection system, which is intended to just react, an intrusion prevention system is intended to prevent malicious events from occurring by preventing attacks as they are happening.